How do Bitcoin Private Keys work?
Though the use of private keys and cryptography may seem complex, it is essential to understand how digital currencies like Bitcoin secure your assets. It is not necessary to have a deep mathematical understanding to grasp the concept of private keys. Let’s begin delving into this topic!
Cryptography
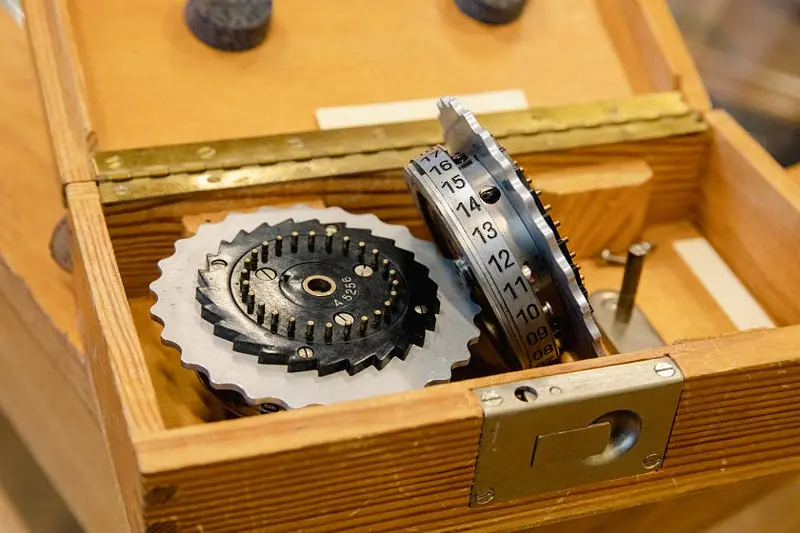
Cryptography is the practice of using various methods to protect sensitive information from being intercepted by unauthorized parties. Throughout history, people have employed different techniques such as codes, ciphers, and secret communication to secure their valuable information, including their financial assets. Today, cryptography is an integral part of the information systems we use daily.
Keys
A key is a set of randomly generated numbers that confirm identity. These keys play a critical role in cryptographic processes, such as encryption, decryption, and message signing, allowing for secure and private communication. In order for cryptography to be effective, it is crucial to safeguard your keys.
Symmetric cryptography
There are two main types of keys used in cryptography: symmetric and asymmetric cryptography.
Symmetric cryptography is a method of secure communication that uses a single secret key to encrypt and decrypt data. It is one of the oldest and most widely used forms of cryptography. The key is used by both the sender and the receiver of the message to encrypt and decrypt the information, as well as for creating and verifying signatures
Symmetric cryptography is used in a wide range of applications, including secure communications, data encryption, and digital signatures. In secure communications, a shared secret key is used to encrypt messages between two parties, ensuring that the messages can only be read by the intended recipient. In data encryption, symmetric cryptography is used to protect sensitive information, such as personal data, credit card numbers, and login credentials. Digital signatures, commonly used in e-commerce and financial transactions, use symmetric cryptography to verify the authenticity of a message or transaction.
Asymmetric cryptography: Public vs. private keys
In contrast, asymmetric cryptography, also known as public key cryptography, utilizes separate keys. A private key is generated and kept secret, while a public key is derived from the private key through a cryptographic function. The private key is used for decrypting data and creating signatures, while the public key is used for encrypting data and verifying signatures.
As long as the private key is kept secure, it can be used to provide cryptographic proof of identity, and the validity of the proof can be verified without ever accessing the private key. Asymmetric cryptography is used in various technologies, such as Bitcoin, email, and end-to-end encrypted messaging apps like Signal.
When spending Bitcoin, you are effectively using your private key to sign a transaction.
Just as a physical signature authenticates a document, digital signatures verify the authenticity of a message and confirm that it has not been altered during transmission. Additionally, digital signatures provide a mathematical proof of identity, which can be used to resolve any disputes between the sender and recipient.
This cryptographic security is why it is imperative to safeguard your private keys. If someone gains access to your private key, they can decrypt messages, forge digital signatures, and spend your Bitcoin without your permission.
Visit our Website
With so many hardware wallets on the market, it can be challenging to choose the right one for your needs. That’s where our Hardware Wallet Comparison TheBitcoinHole.com website comes in. You will find the most comprehensive and honest resource for comparing the features of the top hardware wallets.
Support Us
There are different ways to support our work:
Tip
If you enjoyed this article, you might get value out of these as well!